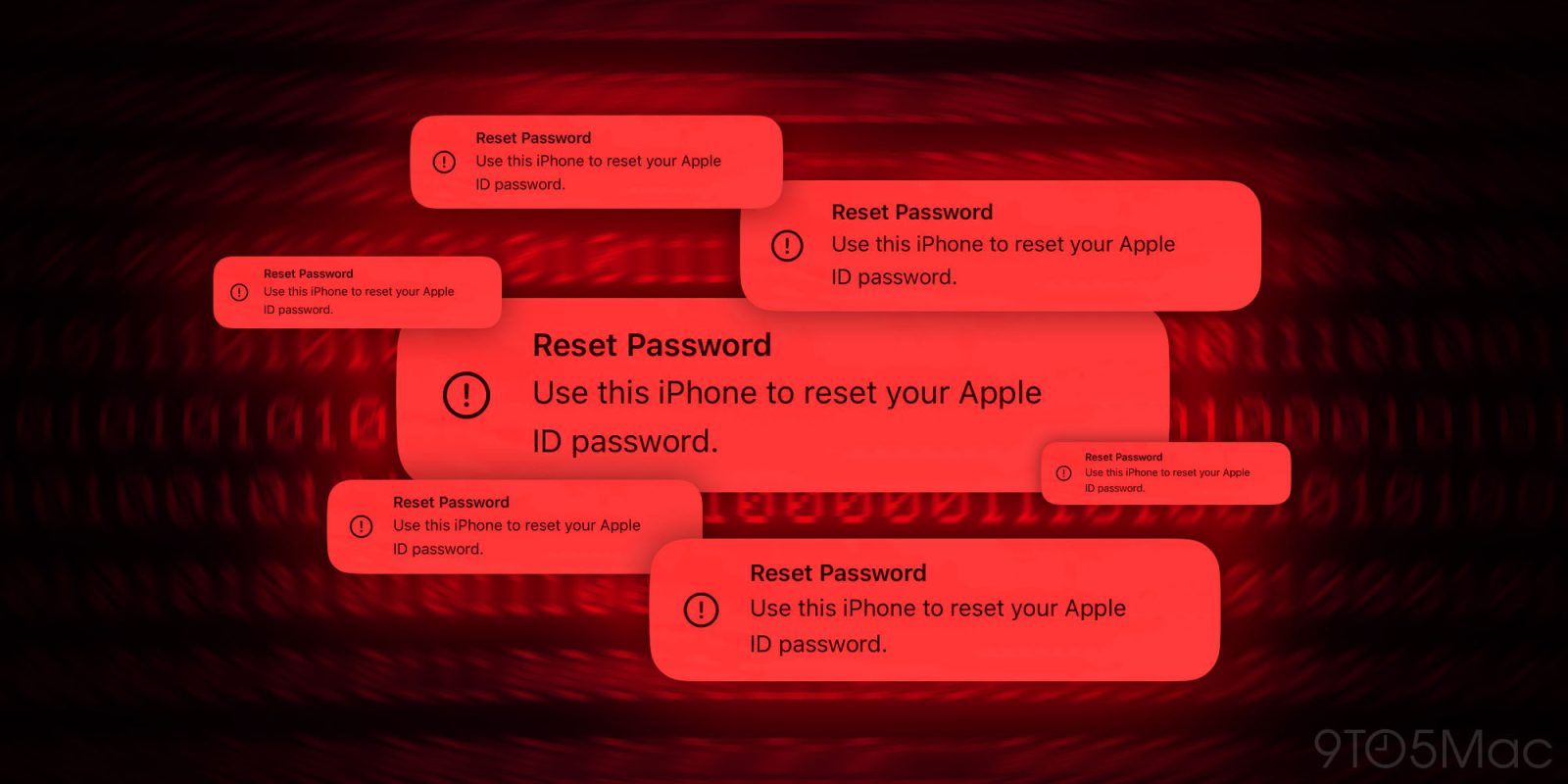
One of many newest assaults on iPhone sees malicious events abuse the Apple ID password reset system to inundate customers with iOS prompts to take over their accounts. Right here’s how one can shield in opposition to iPhone password reset assaults (typically referred to as “MFA bombing”).
We’ve lately heard about Apple customers being focused with MFA bombing (additionally referred to as MFA fatigue or push bombing). It’s not a brand new assault, however it may be a convincing rip-off because it pushes official iOS password reset prompts to victims.
As detailed by Krebs on Safety (by way of Parth Patel), attackers abusing this vulnerability seem like doing so by an Apple consumer’s telephone quantity which may bomb your iPhone and different Apple units with 100+ MFA (multi-factor authentication) system prompts to reset your Apple ID password.
How one can shield in opposition to iPhone password reset assaults
- Decline, decline, decline
- As a result of the reset password requests are a system-level alert, it feels convincing – however be certain that to decide on “Don’t Enable” for all of them
- A technique attackers put on victims down is by bombing them with lots of of prompts, generally over a number of days – hold selecting “Don’t Enable” and optionally use step 3 under
- Notice: In case you see a password reset immediate on the net that could be a unique phishing rip-off, shut the web page as both button may result in a malicious hyperlink
- Don’t reply telephone calls – even when caller ID says “Apple Assist” or comparable
- Attackers are utilizing name spoofing which may make the incoming quantity seem because the official Apple Assist telephone quantity and they are able to confirm private info making the rip-off sound official
- Subsequent, they attempt to get a one-time passcode from you to take over your Apple account
- If in any doubt, decline the decision – and name Apple again (800.275.2273 within the US) – name spoofing shouldn’t have the ability to intercept your outgoing name to the actual Apple
- Apple highlights it is not going to make outbound calls “except the shopper requests to be contacted” and that you must by no means share one-time codes with anybody
- Quickly change your telephone quantity related along with your Apple ID
- In case you proceed to get the prompts, altering your telephone quantity tied to your Apple ID ought to cease them
- Nevertheless, take note this can intrude with iMessage and FaceTime
Extra particulars

As famous in Krebs on Safety’s article, it seems there’s a fee restrict drawback with the Apple ID password reset system.
What sanely designed authentication system would ship dozens of requests for a password change within the span of some moments, when the primary requests haven’t even been acted on by the consumer? May this be the results of a bug in Apple’s techniques?
Hopefully, Apple is engaged on a repair so malicious events can’t abuse this method. However sadly, the password reset rip-off has been highlighted by customers for at the very least two years (doubtless extra).
One current sufferer shared {that a} senior engineer at Apple suggested him to activate the Restoration Key function for his Apple ID to cease the password reset notifications. Nevertheless, in additional testing, that turned out to not be the case and Krebs on Safety verified Apple Restoration Key doesn’t stop reset password prompts.
Associated:
Pictures by 9to5Mac
FTC: We use revenue incomes auto affiliate hyperlinks. Extra.



















