
Getty Pictures
Some of the extensively used community protocols is weak to a newly found assault that may permit adversaries to achieve management over a variety of environments, together with industrial controllers, telecommunications companies, ISPs, and all method of enterprise networks.
Quick for Distant Authentication Dial-In Consumer Service, RADIUS harkens again to the times of dial-in Web and community entry by way of public switched phone networks. It has remained the de facto normal for light-weight authentication ever since and is supported in just about all switches, routers, entry factors, and VPN concentrators shipped prior to now twenty years. Regardless of its early origins, RADIUS stays a necessary staple for managing client-server interactions for:
- VPN entry
- DSL and Fiber to the House connections supplied by ISPs,
- Wi-Fi and 802.1X authentication
- 2G and 3G mobile roaming
- 5G Knowledge Community Identify authentication
- Cell information offloading
- Authentication over non-public APNs for connecting cell gadgets to enterprise networks
- Authentication to crucial infrastructure administration gadgets
- Eduroam and OpenRoaming Wi-Fi
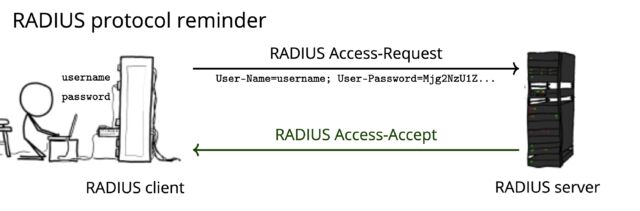
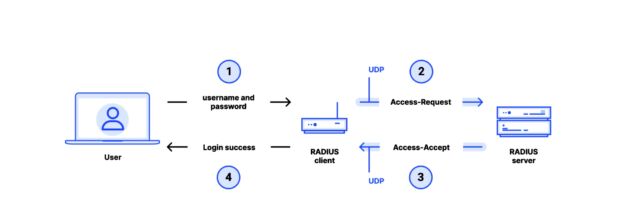
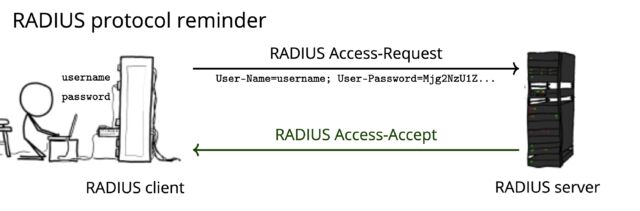
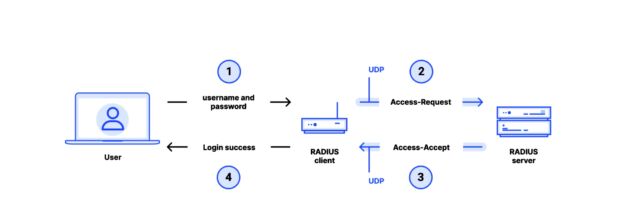
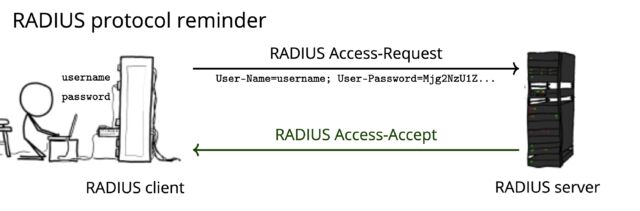
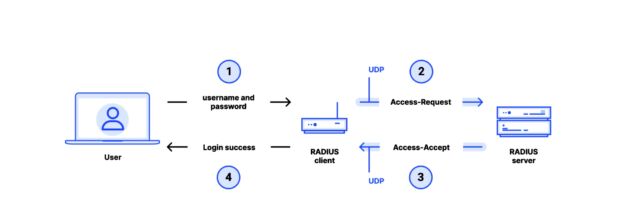
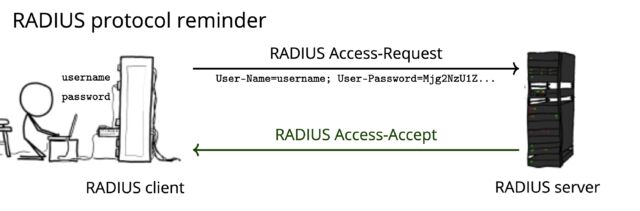
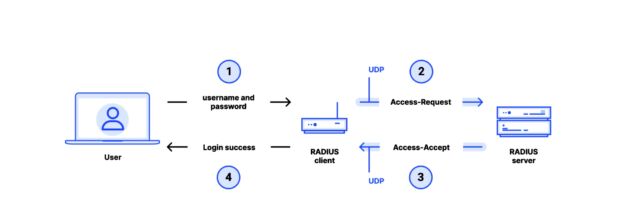
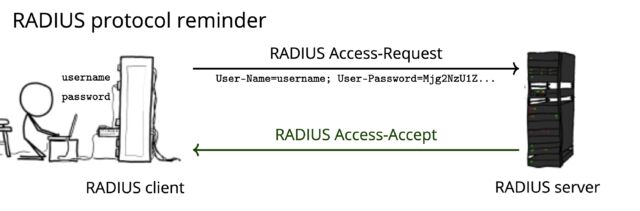
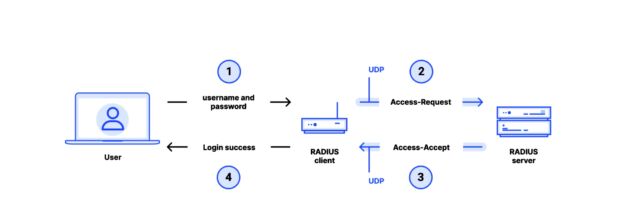
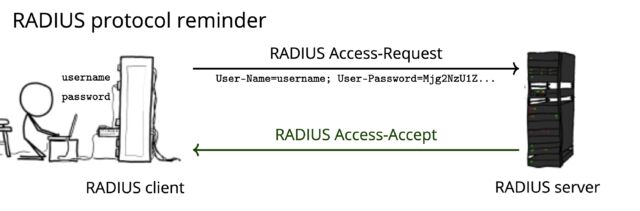
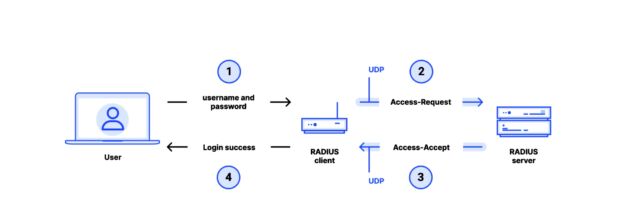
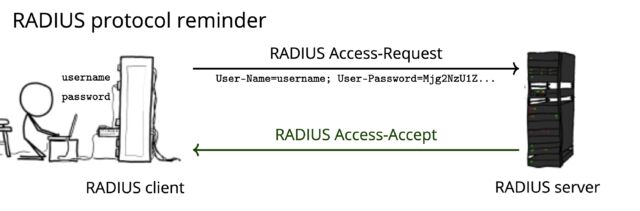
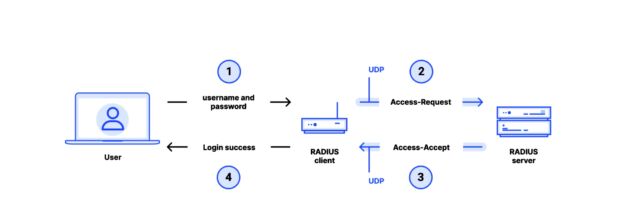
RADIUS supplies seamless interplay between shoppers—sometimes routers, switches, or different home equipment offering community entry—and a central RADIUS server, which acts because the gatekeeper for consumer authentication and entry insurance policies. The aim of RADIUS is to supply centralized authentication, authorization, and accounting administration for distant logins.
The protocol was developed in 1991 by an organization referred to as Livingston Enterprises. In 1997 the Web Engineering Job Drive made it an official normal, which was up to date three years later. Though there’s a draft proposal for sending RADIUS site visitors inside a TLS-encrypted session that is supported by some distributors, many gadgets utilizing the protocol solely ship packets in clear textual content by way of UDP (Consumer Datagram Protocol).
XKCD
Goldberg et al.
Roll-your-own authentication with MD5? For actual?
Since 1994, RADIUS has relied on an improvised, home-grown use of the MD5 hash operate. First created in 1991 and adopted by the IETF in 1992, MD5 was on the time a preferred hash operate for creating what are referred to as “message digests” that map an arbitrary enter like a quantity, textual content, or binary file to a fixed-length 16-byte output.
For a cryptographic hash operate, it needs to be computationally unattainable for an attacker to search out two inputs that map to the identical output. Sadly, MD5 proved to be based mostly on a weak design: Inside just a few years, there have been indicators that the operate could be extra prone than initially thought to attacker-induced collisions, a deadly flaw that permits the attacker to generate two distinct inputs that produce similar outputs. These suspicions had been formally verified in a paper printed in 2004 by researchers Xiaoyun Wang and Hongbo Yu and additional refined in a analysis paper printed three years later.
The latter paper—printed in 2007 by researchers Marc Stevens, Arjen Lenstra, and Benne de Weger—described what’s referred to as a chosen-prefix collision, a sort of collision that outcomes from two messages chosen by an attacker that, when mixed with two extra messages, create the identical hash. That’s, the adversary freely chooses two distinct enter prefixes 𝑃 and 𝑃′ of arbitrary content material that, when mixed with rigorously corresponding suffixes 𝑆 and 𝑆′ that resemble random gibberish, generate the identical hash. In mathematical notation, such a chosen-prefix collision can be written as 𝐻(𝑃‖𝑆)=𝐻(𝑃′‖𝑆′). The sort of collision assault is rather more highly effective as a result of it permits the attacker the liberty to create extremely custom-made forgeries.
For example the practicality and devastating penalties of the assault, Stevens, Lenstra, and de Weger used it to create two cryptographic X.509 certificates that generated the identical MD5 signature however totally different public keys and totally different Distinguished Identify fields. Such a collision may induce a certificates authority aspiring to signal a certificates for one area to unknowingly signal a certificates for a completely totally different, malicious area.
In 2008, a group of researchers that included Stevens, Lenstra, and de Weger demonstrated how a selected prefix assault on MD5 allowed them to create a rogue certificates authority that might generate TLS certificates that may be trusted by all main browsers. A key ingredient for the assault is software program named hashclash, developed by the researchers. Hashclash has since been made publicly accessible.
Regardless of the undisputed demise of MD5, the operate remained in widespread use for years. Deprecation of MD5 didn’t begin in earnest till 2012 after malware referred to as Flame, reportedly created collectively by the governments of Israel and the US, was discovered to have used a selected prefix assault to spoof MD5-based code signing by Microsoft’s Home windows replace mechanism. Flame used the collision-enabled spoofing to hijack the replace mechanism so the malware may unfold from system to system inside an contaminated community.
Greater than 12 years after Flame’s devastating injury was found and twenty years after collision susceptibility was confirmed, MD5 has felled one more extensively deployed know-how that has resisted frequent knowledge to maneuver away from the hashing scheme—the RADIUS protocol, which is supported in {hardware} or software program offered by at the very least 86 distinct distributors. The result’s “Blast RADIUS,” a fancy assault that permits an attacker with an energetic adversary-in-the-middle place to achieve administrator entry to gadgets that use RADIUS to authenticate themselves to a server.
“Surprisingly, within the twenty years since Wang et al. demonstrated an MD5 hash collision in 2004, RADIUS has not been up to date to take away MD5,” the analysis group behind Blast RADIUS wrote in a paper printed Tuesday and titled RADIUS/UDP Thought-about Dangerous. “In reality, RADIUS seems to have obtained notably little safety evaluation given its ubiquity in fashionable networks.”
The paper’s publication is being coordinated with safety bulletins from at the very least 90 distributors whose wares are weak. Most of the bulletins are accompanied by patches implementing short-term fixes, whereas a working group of engineers throughout the business drafts longer-term options. Anybody who makes use of {hardware} or software program that comes with RADIUS ought to learn the technical particulars offered later on this publish and examine with the producer for safety steering.

Getty Pictures
Some of the extensively used community protocols is weak to a newly found assault that may permit adversaries to achieve management over a variety of environments, together with industrial controllers, telecommunications companies, ISPs, and all method of enterprise networks.
Quick for Distant Authentication Dial-In Consumer Service, RADIUS harkens again to the times of dial-in Web and community entry by way of public switched phone networks. It has remained the de facto normal for light-weight authentication ever since and is supported in just about all switches, routers, entry factors, and VPN concentrators shipped prior to now twenty years. Regardless of its early origins, RADIUS stays a necessary staple for managing client-server interactions for:
- VPN entry
- DSL and Fiber to the House connections supplied by ISPs,
- Wi-Fi and 802.1X authentication
- 2G and 3G mobile roaming
- 5G Knowledge Community Identify authentication
- Cell information offloading
- Authentication over non-public APNs for connecting cell gadgets to enterprise networks
- Authentication to crucial infrastructure administration gadgets
- Eduroam and OpenRoaming Wi-Fi
RADIUS supplies seamless interplay between shoppers—sometimes routers, switches, or different home equipment offering community entry—and a central RADIUS server, which acts because the gatekeeper for consumer authentication and entry insurance policies. The aim of RADIUS is to supply centralized authentication, authorization, and accounting administration for distant logins.
The protocol was developed in 1991 by an organization referred to as Livingston Enterprises. In 1997 the Web Engineering Job Drive made it an official normal, which was up to date three years later. Though there’s a draft proposal for sending RADIUS site visitors inside a TLS-encrypted session that is supported by some distributors, many gadgets utilizing the protocol solely ship packets in clear textual content by way of UDP (Consumer Datagram Protocol).
XKCD
Goldberg et al.
Roll-your-own authentication with MD5? For actual?
Since 1994, RADIUS has relied on an improvised, home-grown use of the MD5 hash operate. First created in 1991 and adopted by the IETF in 1992, MD5 was on the time a preferred hash operate for creating what are referred to as “message digests” that map an arbitrary enter like a quantity, textual content, or binary file to a fixed-length 16-byte output.
For a cryptographic hash operate, it needs to be computationally unattainable for an attacker to search out two inputs that map to the identical output. Sadly, MD5 proved to be based mostly on a weak design: Inside just a few years, there have been indicators that the operate could be extra prone than initially thought to attacker-induced collisions, a deadly flaw that permits the attacker to generate two distinct inputs that produce similar outputs. These suspicions had been formally verified in a paper printed in 2004 by researchers Xiaoyun Wang and Hongbo Yu and additional refined in a analysis paper printed three years later.
The latter paper—printed in 2007 by researchers Marc Stevens, Arjen Lenstra, and Benne de Weger—described what’s referred to as a chosen-prefix collision, a sort of collision that outcomes from two messages chosen by an attacker that, when mixed with two extra messages, create the identical hash. That’s, the adversary freely chooses two distinct enter prefixes 𝑃 and 𝑃′ of arbitrary content material that, when mixed with rigorously corresponding suffixes 𝑆 and 𝑆′ that resemble random gibberish, generate the identical hash. In mathematical notation, such a chosen-prefix collision can be written as 𝐻(𝑃‖𝑆)=𝐻(𝑃′‖𝑆′). The sort of collision assault is rather more highly effective as a result of it permits the attacker the liberty to create extremely custom-made forgeries.
For example the practicality and devastating penalties of the assault, Stevens, Lenstra, and de Weger used it to create two cryptographic X.509 certificates that generated the identical MD5 signature however totally different public keys and totally different Distinguished Identify fields. Such a collision may induce a certificates authority aspiring to signal a certificates for one area to unknowingly signal a certificates for a completely totally different, malicious area.
In 2008, a group of researchers that included Stevens, Lenstra, and de Weger demonstrated how a selected prefix assault on MD5 allowed them to create a rogue certificates authority that might generate TLS certificates that may be trusted by all main browsers. A key ingredient for the assault is software program named hashclash, developed by the researchers. Hashclash has since been made publicly accessible.
Regardless of the undisputed demise of MD5, the operate remained in widespread use for years. Deprecation of MD5 didn’t begin in earnest till 2012 after malware referred to as Flame, reportedly created collectively by the governments of Israel and the US, was discovered to have used a selected prefix assault to spoof MD5-based code signing by Microsoft’s Home windows replace mechanism. Flame used the collision-enabled spoofing to hijack the replace mechanism so the malware may unfold from system to system inside an contaminated community.
Greater than 12 years after Flame’s devastating injury was found and twenty years after collision susceptibility was confirmed, MD5 has felled one more extensively deployed know-how that has resisted frequent knowledge to maneuver away from the hashing scheme—the RADIUS protocol, which is supported in {hardware} or software program offered by at the very least 86 distinct distributors. The result’s “Blast RADIUS,” a fancy assault that permits an attacker with an energetic adversary-in-the-middle place to achieve administrator entry to gadgets that use RADIUS to authenticate themselves to a server.
“Surprisingly, within the twenty years since Wang et al. demonstrated an MD5 hash collision in 2004, RADIUS has not been up to date to take away MD5,” the analysis group behind Blast RADIUS wrote in a paper printed Tuesday and titled RADIUS/UDP Thought-about Dangerous. “In reality, RADIUS seems to have obtained notably little safety evaluation given its ubiquity in fashionable networks.”
The paper’s publication is being coordinated with safety bulletins from at the very least 90 distributors whose wares are weak. Most of the bulletins are accompanied by patches implementing short-term fixes, whereas a working group of engineers throughout the business drafts longer-term options. Anybody who makes use of {hardware} or software program that comes with RADIUS ought to learn the technical particulars offered later on this publish and examine with the producer for safety steering.

Getty Pictures
Some of the extensively used community protocols is weak to a newly found assault that may permit adversaries to achieve management over a variety of environments, together with industrial controllers, telecommunications companies, ISPs, and all method of enterprise networks.
Quick for Distant Authentication Dial-In Consumer Service, RADIUS harkens again to the times of dial-in Web and community entry by way of public switched phone networks. It has remained the de facto normal for light-weight authentication ever since and is supported in just about all switches, routers, entry factors, and VPN concentrators shipped prior to now twenty years. Regardless of its early origins, RADIUS stays a necessary staple for managing client-server interactions for:
- VPN entry
- DSL and Fiber to the House connections supplied by ISPs,
- Wi-Fi and 802.1X authentication
- 2G and 3G mobile roaming
- 5G Knowledge Community Identify authentication
- Cell information offloading
- Authentication over non-public APNs for connecting cell gadgets to enterprise networks
- Authentication to crucial infrastructure administration gadgets
- Eduroam and OpenRoaming Wi-Fi
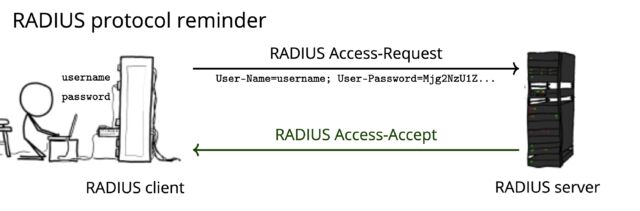
RADIUS supplies seamless interplay between shoppers—sometimes routers, switches, or different home equipment offering community entry—and a central RADIUS server, which acts because the gatekeeper for consumer authentication and entry insurance policies. The aim of RADIUS is to supply centralized authentication, authorization, and accounting administration for distant logins.
The protocol was developed in 1991 by an organization referred to as Livingston Enterprises. In 1997 the Web Engineering Job Drive made it an official normal, which was up to date three years later. Though there’s a draft proposal for sending RADIUS site visitors inside a TLS-encrypted session that is supported by some distributors, many gadgets utilizing the protocol solely ship packets in clear textual content by way of UDP (Consumer Datagram Protocol).
XKCD
Goldberg et al.
Roll-your-own authentication with MD5? For actual?
Since 1994, RADIUS has relied on an improvised, home-grown use of the MD5 hash operate. First created in 1991 and adopted by the IETF in 1992, MD5 was on the time a preferred hash operate for creating what are referred to as “message digests” that map an arbitrary enter like a quantity, textual content, or binary file to a fixed-length 16-byte output.
For a cryptographic hash operate, it needs to be computationally unattainable for an attacker to search out two inputs that map to the identical output. Sadly, MD5 proved to be based mostly on a weak design: Inside just a few years, there have been indicators that the operate could be extra prone than initially thought to attacker-induced collisions, a deadly flaw that permits the attacker to generate two distinct inputs that produce similar outputs. These suspicions had been formally verified in a paper printed in 2004 by researchers Xiaoyun Wang and Hongbo Yu and additional refined in a analysis paper printed three years later.
The latter paper—printed in 2007 by researchers Marc Stevens, Arjen Lenstra, and Benne de Weger—described what’s referred to as a chosen-prefix collision, a sort of collision that outcomes from two messages chosen by an attacker that, when mixed with two extra messages, create the identical hash. That’s, the adversary freely chooses two distinct enter prefixes 𝑃 and 𝑃′ of arbitrary content material that, when mixed with rigorously corresponding suffixes 𝑆 and 𝑆′ that resemble random gibberish, generate the identical hash. In mathematical notation, such a chosen-prefix collision can be written as 𝐻(𝑃‖𝑆)=𝐻(𝑃′‖𝑆′). The sort of collision assault is rather more highly effective as a result of it permits the attacker the liberty to create extremely custom-made forgeries.
For example the practicality and devastating penalties of the assault, Stevens, Lenstra, and de Weger used it to create two cryptographic X.509 certificates that generated the identical MD5 signature however totally different public keys and totally different Distinguished Identify fields. Such a collision may induce a certificates authority aspiring to signal a certificates for one area to unknowingly signal a certificates for a completely totally different, malicious area.
In 2008, a group of researchers that included Stevens, Lenstra, and de Weger demonstrated how a selected prefix assault on MD5 allowed them to create a rogue certificates authority that might generate TLS certificates that may be trusted by all main browsers. A key ingredient for the assault is software program named hashclash, developed by the researchers. Hashclash has since been made publicly accessible.
Regardless of the undisputed demise of MD5, the operate remained in widespread use for years. Deprecation of MD5 didn’t begin in earnest till 2012 after malware referred to as Flame, reportedly created collectively by the governments of Israel and the US, was discovered to have used a selected prefix assault to spoof MD5-based code signing by Microsoft’s Home windows replace mechanism. Flame used the collision-enabled spoofing to hijack the replace mechanism so the malware may unfold from system to system inside an contaminated community.
Greater than 12 years after Flame’s devastating injury was found and twenty years after collision susceptibility was confirmed, MD5 has felled one more extensively deployed know-how that has resisted frequent knowledge to maneuver away from the hashing scheme—the RADIUS protocol, which is supported in {hardware} or software program offered by at the very least 86 distinct distributors. The result’s “Blast RADIUS,” a fancy assault that permits an attacker with an energetic adversary-in-the-middle place to achieve administrator entry to gadgets that use RADIUS to authenticate themselves to a server.
“Surprisingly, within the twenty years since Wang et al. demonstrated an MD5 hash collision in 2004, RADIUS has not been up to date to take away MD5,” the analysis group behind Blast RADIUS wrote in a paper printed Tuesday and titled RADIUS/UDP Thought-about Dangerous. “In reality, RADIUS seems to have obtained notably little safety evaluation given its ubiquity in fashionable networks.”
The paper’s publication is being coordinated with safety bulletins from at the very least 90 distributors whose wares are weak. Most of the bulletins are accompanied by patches implementing short-term fixes, whereas a working group of engineers throughout the business drafts longer-term options. Anybody who makes use of {hardware} or software program that comes with RADIUS ought to learn the technical particulars offered later on this publish and examine with the producer for safety steering.

Getty Pictures
Some of the extensively used community protocols is weak to a newly found assault that may permit adversaries to achieve management over a variety of environments, together with industrial controllers, telecommunications companies, ISPs, and all method of enterprise networks.
Quick for Distant Authentication Dial-In Consumer Service, RADIUS harkens again to the times of dial-in Web and community entry by way of public switched phone networks. It has remained the de facto normal for light-weight authentication ever since and is supported in just about all switches, routers, entry factors, and VPN concentrators shipped prior to now twenty years. Regardless of its early origins, RADIUS stays a necessary staple for managing client-server interactions for:
- VPN entry
- DSL and Fiber to the House connections supplied by ISPs,
- Wi-Fi and 802.1X authentication
- 2G and 3G mobile roaming
- 5G Knowledge Community Identify authentication
- Cell information offloading
- Authentication over non-public APNs for connecting cell gadgets to enterprise networks
- Authentication to crucial infrastructure administration gadgets
- Eduroam and OpenRoaming Wi-Fi
RADIUS supplies seamless interplay between shoppers—sometimes routers, switches, or different home equipment offering community entry—and a central RADIUS server, which acts because the gatekeeper for consumer authentication and entry insurance policies. The aim of RADIUS is to supply centralized authentication, authorization, and accounting administration for distant logins.
The protocol was developed in 1991 by an organization referred to as Livingston Enterprises. In 1997 the Web Engineering Job Drive made it an official normal, which was up to date three years later. Though there’s a draft proposal for sending RADIUS site visitors inside a TLS-encrypted session that is supported by some distributors, many gadgets utilizing the protocol solely ship packets in clear textual content by way of UDP (Consumer Datagram Protocol).
XKCD
Goldberg et al.
Roll-your-own authentication with MD5? For actual?
Since 1994, RADIUS has relied on an improvised, home-grown use of the MD5 hash operate. First created in 1991 and adopted by the IETF in 1992, MD5 was on the time a preferred hash operate for creating what are referred to as “message digests” that map an arbitrary enter like a quantity, textual content, or binary file to a fixed-length 16-byte output.
For a cryptographic hash operate, it needs to be computationally unattainable for an attacker to search out two inputs that map to the identical output. Sadly, MD5 proved to be based mostly on a weak design: Inside just a few years, there have been indicators that the operate could be extra prone than initially thought to attacker-induced collisions, a deadly flaw that permits the attacker to generate two distinct inputs that produce similar outputs. These suspicions had been formally verified in a paper printed in 2004 by researchers Xiaoyun Wang and Hongbo Yu and additional refined in a analysis paper printed three years later.
The latter paper—printed in 2007 by researchers Marc Stevens, Arjen Lenstra, and Benne de Weger—described what’s referred to as a chosen-prefix collision, a sort of collision that outcomes from two messages chosen by an attacker that, when mixed with two extra messages, create the identical hash. That’s, the adversary freely chooses two distinct enter prefixes 𝑃 and 𝑃′ of arbitrary content material that, when mixed with rigorously corresponding suffixes 𝑆 and 𝑆′ that resemble random gibberish, generate the identical hash. In mathematical notation, such a chosen-prefix collision can be written as 𝐻(𝑃‖𝑆)=𝐻(𝑃′‖𝑆′). The sort of collision assault is rather more highly effective as a result of it permits the attacker the liberty to create extremely custom-made forgeries.
For example the practicality and devastating penalties of the assault, Stevens, Lenstra, and de Weger used it to create two cryptographic X.509 certificates that generated the identical MD5 signature however totally different public keys and totally different Distinguished Identify fields. Such a collision may induce a certificates authority aspiring to signal a certificates for one area to unknowingly signal a certificates for a completely totally different, malicious area.
In 2008, a group of researchers that included Stevens, Lenstra, and de Weger demonstrated how a selected prefix assault on MD5 allowed them to create a rogue certificates authority that might generate TLS certificates that may be trusted by all main browsers. A key ingredient for the assault is software program named hashclash, developed by the researchers. Hashclash has since been made publicly accessible.
Regardless of the undisputed demise of MD5, the operate remained in widespread use for years. Deprecation of MD5 didn’t begin in earnest till 2012 after malware referred to as Flame, reportedly created collectively by the governments of Israel and the US, was discovered to have used a selected prefix assault to spoof MD5-based code signing by Microsoft’s Home windows replace mechanism. Flame used the collision-enabled spoofing to hijack the replace mechanism so the malware may unfold from system to system inside an contaminated community.
Greater than 12 years after Flame’s devastating injury was found and twenty years after collision susceptibility was confirmed, MD5 has felled one more extensively deployed know-how that has resisted frequent knowledge to maneuver away from the hashing scheme—the RADIUS protocol, which is supported in {hardware} or software program offered by at the very least 86 distinct distributors. The result’s “Blast RADIUS,” a fancy assault that permits an attacker with an energetic adversary-in-the-middle place to achieve administrator entry to gadgets that use RADIUS to authenticate themselves to a server.
“Surprisingly, within the twenty years since Wang et al. demonstrated an MD5 hash collision in 2004, RADIUS has not been up to date to take away MD5,” the analysis group behind Blast RADIUS wrote in a paper printed Tuesday and titled RADIUS/UDP Thought-about Dangerous. “In reality, RADIUS seems to have obtained notably little safety evaluation given its ubiquity in fashionable networks.”
The paper’s publication is being coordinated with safety bulletins from at the very least 90 distributors whose wares are weak. Most of the bulletins are accompanied by patches implementing short-term fixes, whereas a working group of engineers throughout the business drafts longer-term options. Anybody who makes use of {hardware} or software program that comes with RADIUS ought to learn the technical particulars offered later on this publish and examine with the producer for safety steering.

Getty Pictures
Some of the extensively used community protocols is weak to a newly found assault that may permit adversaries to achieve management over a variety of environments, together with industrial controllers, telecommunications companies, ISPs, and all method of enterprise networks.
Quick for Distant Authentication Dial-In Consumer Service, RADIUS harkens again to the times of dial-in Web and community entry by way of public switched phone networks. It has remained the de facto normal for light-weight authentication ever since and is supported in just about all switches, routers, entry factors, and VPN concentrators shipped prior to now twenty years. Regardless of its early origins, RADIUS stays a necessary staple for managing client-server interactions for:
- VPN entry
- DSL and Fiber to the House connections supplied by ISPs,
- Wi-Fi and 802.1X authentication
- 2G and 3G mobile roaming
- 5G Knowledge Community Identify authentication
- Cell information offloading
- Authentication over non-public APNs for connecting cell gadgets to enterprise networks
- Authentication to crucial infrastructure administration gadgets
- Eduroam and OpenRoaming Wi-Fi
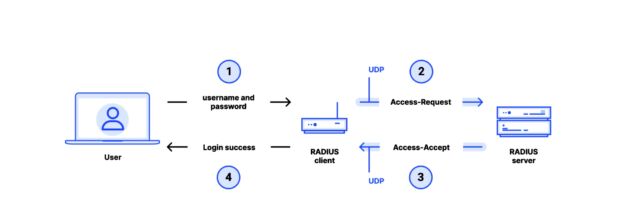
RADIUS supplies seamless interplay between shoppers—sometimes routers, switches, or different home equipment offering community entry—and a central RADIUS server, which acts because the gatekeeper for consumer authentication and entry insurance policies. The aim of RADIUS is to supply centralized authentication, authorization, and accounting administration for distant logins.
The protocol was developed in 1991 by an organization referred to as Livingston Enterprises. In 1997 the Web Engineering Job Drive made it an official normal, which was up to date three years later. Though there’s a draft proposal for sending RADIUS site visitors inside a TLS-encrypted session that is supported by some distributors, many gadgets utilizing the protocol solely ship packets in clear textual content by way of UDP (Consumer Datagram Protocol).
XKCD
Goldberg et al.
Roll-your-own authentication with MD5? For actual?
Since 1994, RADIUS has relied on an improvised, home-grown use of the MD5 hash operate. First created in 1991 and adopted by the IETF in 1992, MD5 was on the time a preferred hash operate for creating what are referred to as “message digests” that map an arbitrary enter like a quantity, textual content, or binary file to a fixed-length 16-byte output.
For a cryptographic hash operate, it needs to be computationally unattainable for an attacker to search out two inputs that map to the identical output. Sadly, MD5 proved to be based mostly on a weak design: Inside just a few years, there have been indicators that the operate could be extra prone than initially thought to attacker-induced collisions, a deadly flaw that permits the attacker to generate two distinct inputs that produce similar outputs. These suspicions had been formally verified in a paper printed in 2004 by researchers Xiaoyun Wang and Hongbo Yu and additional refined in a analysis paper printed three years later.
The latter paper—printed in 2007 by researchers Marc Stevens, Arjen Lenstra, and Benne de Weger—described what’s referred to as a chosen-prefix collision, a sort of collision that outcomes from two messages chosen by an attacker that, when mixed with two extra messages, create the identical hash. That’s, the adversary freely chooses two distinct enter prefixes 𝑃 and 𝑃′ of arbitrary content material that, when mixed with rigorously corresponding suffixes 𝑆 and 𝑆′ that resemble random gibberish, generate the identical hash. In mathematical notation, such a chosen-prefix collision can be written as 𝐻(𝑃‖𝑆)=𝐻(𝑃′‖𝑆′). The sort of collision assault is rather more highly effective as a result of it permits the attacker the liberty to create extremely custom-made forgeries.
For example the practicality and devastating penalties of the assault, Stevens, Lenstra, and de Weger used it to create two cryptographic X.509 certificates that generated the identical MD5 signature however totally different public keys and totally different Distinguished Identify fields. Such a collision may induce a certificates authority aspiring to signal a certificates for one area to unknowingly signal a certificates for a completely totally different, malicious area.
In 2008, a group of researchers that included Stevens, Lenstra, and de Weger demonstrated how a selected prefix assault on MD5 allowed them to create a rogue certificates authority that might generate TLS certificates that may be trusted by all main browsers. A key ingredient for the assault is software program named hashclash, developed by the researchers. Hashclash has since been made publicly accessible.
Regardless of the undisputed demise of MD5, the operate remained in widespread use for years. Deprecation of MD5 didn’t begin in earnest till 2012 after malware referred to as Flame, reportedly created collectively by the governments of Israel and the US, was discovered to have used a selected prefix assault to spoof MD5-based code signing by Microsoft’s Home windows replace mechanism. Flame used the collision-enabled spoofing to hijack the replace mechanism so the malware may unfold from system to system inside an contaminated community.
Greater than 12 years after Flame’s devastating injury was found and twenty years after collision susceptibility was confirmed, MD5 has felled one more extensively deployed know-how that has resisted frequent knowledge to maneuver away from the hashing scheme—the RADIUS protocol, which is supported in {hardware} or software program offered by at the very least 86 distinct distributors. The result’s “Blast RADIUS,” a fancy assault that permits an attacker with an energetic adversary-in-the-middle place to achieve administrator entry to gadgets that use RADIUS to authenticate themselves to a server.
“Surprisingly, within the twenty years since Wang et al. demonstrated an MD5 hash collision in 2004, RADIUS has not been up to date to take away MD5,” the analysis group behind Blast RADIUS wrote in a paper printed Tuesday and titled RADIUS/UDP Thought-about Dangerous. “In reality, RADIUS seems to have obtained notably little safety evaluation given its ubiquity in fashionable networks.”
The paper’s publication is being coordinated with safety bulletins from at the very least 90 distributors whose wares are weak. Most of the bulletins are accompanied by patches implementing short-term fixes, whereas a working group of engineers throughout the business drafts longer-term options. Anybody who makes use of {hardware} or software program that comes with RADIUS ought to learn the technical particulars offered later on this publish and examine with the producer for safety steering.

Getty Pictures
Some of the extensively used community protocols is weak to a newly found assault that may permit adversaries to achieve management over a variety of environments, together with industrial controllers, telecommunications companies, ISPs, and all method of enterprise networks.
Quick for Distant Authentication Dial-In Consumer Service, RADIUS harkens again to the times of dial-in Web and community entry by way of public switched phone networks. It has remained the de facto normal for light-weight authentication ever since and is supported in just about all switches, routers, entry factors, and VPN concentrators shipped prior to now twenty years. Regardless of its early origins, RADIUS stays a necessary staple for managing client-server interactions for:
- VPN entry
- DSL and Fiber to the House connections supplied by ISPs,
- Wi-Fi and 802.1X authentication
- 2G and 3G mobile roaming
- 5G Knowledge Community Identify authentication
- Cell information offloading
- Authentication over non-public APNs for connecting cell gadgets to enterprise networks
- Authentication to crucial infrastructure administration gadgets
- Eduroam and OpenRoaming Wi-Fi
RADIUS supplies seamless interplay between shoppers—sometimes routers, switches, or different home equipment offering community entry—and a central RADIUS server, which acts because the gatekeeper for consumer authentication and entry insurance policies. The aim of RADIUS is to supply centralized authentication, authorization, and accounting administration for distant logins.
The protocol was developed in 1991 by an organization referred to as Livingston Enterprises. In 1997 the Web Engineering Job Drive made it an official normal, which was up to date three years later. Though there’s a draft proposal for sending RADIUS site visitors inside a TLS-encrypted session that is supported by some distributors, many gadgets utilizing the protocol solely ship packets in clear textual content by way of UDP (Consumer Datagram Protocol).
XKCD
Goldberg et al.
Roll-your-own authentication with MD5? For actual?
Since 1994, RADIUS has relied on an improvised, home-grown use of the MD5 hash operate. First created in 1991 and adopted by the IETF in 1992, MD5 was on the time a preferred hash operate for creating what are referred to as “message digests” that map an arbitrary enter like a quantity, textual content, or binary file to a fixed-length 16-byte output.
For a cryptographic hash operate, it needs to be computationally unattainable for an attacker to search out two inputs that map to the identical output. Sadly, MD5 proved to be based mostly on a weak design: Inside just a few years, there have been indicators that the operate could be extra prone than initially thought to attacker-induced collisions, a deadly flaw that permits the attacker to generate two distinct inputs that produce similar outputs. These suspicions had been formally verified in a paper printed in 2004 by researchers Xiaoyun Wang and Hongbo Yu and additional refined in a analysis paper printed three years later.
The latter paper—printed in 2007 by researchers Marc Stevens, Arjen Lenstra, and Benne de Weger—described what’s referred to as a chosen-prefix collision, a sort of collision that outcomes from two messages chosen by an attacker that, when mixed with two extra messages, create the identical hash. That’s, the adversary freely chooses two distinct enter prefixes 𝑃 and 𝑃′ of arbitrary content material that, when mixed with rigorously corresponding suffixes 𝑆 and 𝑆′ that resemble random gibberish, generate the identical hash. In mathematical notation, such a chosen-prefix collision can be written as 𝐻(𝑃‖𝑆)=𝐻(𝑃′‖𝑆′). The sort of collision assault is rather more highly effective as a result of it permits the attacker the liberty to create extremely custom-made forgeries.
For example the practicality and devastating penalties of the assault, Stevens, Lenstra, and de Weger used it to create two cryptographic X.509 certificates that generated the identical MD5 signature however totally different public keys and totally different Distinguished Identify fields. Such a collision may induce a certificates authority aspiring to signal a certificates for one area to unknowingly signal a certificates for a completely totally different, malicious area.
In 2008, a group of researchers that included Stevens, Lenstra, and de Weger demonstrated how a selected prefix assault on MD5 allowed them to create a rogue certificates authority that might generate TLS certificates that may be trusted by all main browsers. A key ingredient for the assault is software program named hashclash, developed by the researchers. Hashclash has since been made publicly accessible.
Regardless of the undisputed demise of MD5, the operate remained in widespread use for years. Deprecation of MD5 didn’t begin in earnest till 2012 after malware referred to as Flame, reportedly created collectively by the governments of Israel and the US, was discovered to have used a selected prefix assault to spoof MD5-based code signing by Microsoft’s Home windows replace mechanism. Flame used the collision-enabled spoofing to hijack the replace mechanism so the malware may unfold from system to system inside an contaminated community.
Greater than 12 years after Flame’s devastating injury was found and twenty years after collision susceptibility was confirmed, MD5 has felled one more extensively deployed know-how that has resisted frequent knowledge to maneuver away from the hashing scheme—the RADIUS protocol, which is supported in {hardware} or software program offered by at the very least 86 distinct distributors. The result’s “Blast RADIUS,” a fancy assault that permits an attacker with an energetic adversary-in-the-middle place to achieve administrator entry to gadgets that use RADIUS to authenticate themselves to a server.
“Surprisingly, within the twenty years since Wang et al. demonstrated an MD5 hash collision in 2004, RADIUS has not been up to date to take away MD5,” the analysis group behind Blast RADIUS wrote in a paper printed Tuesday and titled RADIUS/UDP Thought-about Dangerous. “In reality, RADIUS seems to have obtained notably little safety evaluation given its ubiquity in fashionable networks.”
The paper’s publication is being coordinated with safety bulletins from at the very least 90 distributors whose wares are weak. Most of the bulletins are accompanied by patches implementing short-term fixes, whereas a working group of engineers throughout the business drafts longer-term options. Anybody who makes use of {hardware} or software program that comes with RADIUS ought to learn the technical particulars offered later on this publish and examine with the producer for safety steering.

Getty Pictures
Some of the extensively used community protocols is weak to a newly found assault that may permit adversaries to achieve management over a variety of environments, together with industrial controllers, telecommunications companies, ISPs, and all method of enterprise networks.
Quick for Distant Authentication Dial-In Consumer Service, RADIUS harkens again to the times of dial-in Web and community entry by way of public switched phone networks. It has remained the de facto normal for light-weight authentication ever since and is supported in just about all switches, routers, entry factors, and VPN concentrators shipped prior to now twenty years. Regardless of its early origins, RADIUS stays a necessary staple for managing client-server interactions for:
- VPN entry
- DSL and Fiber to the House connections supplied by ISPs,
- Wi-Fi and 802.1X authentication
- 2G and 3G mobile roaming
- 5G Knowledge Community Identify authentication
- Cell information offloading
- Authentication over non-public APNs for connecting cell gadgets to enterprise networks
- Authentication to crucial infrastructure administration gadgets
- Eduroam and OpenRoaming Wi-Fi
RADIUS supplies seamless interplay between shoppers—sometimes routers, switches, or different home equipment offering community entry—and a central RADIUS server, which acts because the gatekeeper for consumer authentication and entry insurance policies. The aim of RADIUS is to supply centralized authentication, authorization, and accounting administration for distant logins.
The protocol was developed in 1991 by an organization referred to as Livingston Enterprises. In 1997 the Web Engineering Job Drive made it an official normal, which was up to date three years later. Though there’s a draft proposal for sending RADIUS site visitors inside a TLS-encrypted session that is supported by some distributors, many gadgets utilizing the protocol solely ship packets in clear textual content by way of UDP (Consumer Datagram Protocol).
XKCD
Goldberg et al.
Roll-your-own authentication with MD5? For actual?
Since 1994, RADIUS has relied on an improvised, home-grown use of the MD5 hash operate. First created in 1991 and adopted by the IETF in 1992, MD5 was on the time a preferred hash operate for creating what are referred to as “message digests” that map an arbitrary enter like a quantity, textual content, or binary file to a fixed-length 16-byte output.
For a cryptographic hash operate, it needs to be computationally unattainable for an attacker to search out two inputs that map to the identical output. Sadly, MD5 proved to be based mostly on a weak design: Inside just a few years, there have been indicators that the operate could be extra prone than initially thought to attacker-induced collisions, a deadly flaw that permits the attacker to generate two distinct inputs that produce similar outputs. These suspicions had been formally verified in a paper printed in 2004 by researchers Xiaoyun Wang and Hongbo Yu and additional refined in a analysis paper printed three years later.
The latter paper—printed in 2007 by researchers Marc Stevens, Arjen Lenstra, and Benne de Weger—described what’s referred to as a chosen-prefix collision, a sort of collision that outcomes from two messages chosen by an attacker that, when mixed with two extra messages, create the identical hash. That’s, the adversary freely chooses two distinct enter prefixes 𝑃 and 𝑃′ of arbitrary content material that, when mixed with rigorously corresponding suffixes 𝑆 and 𝑆′ that resemble random gibberish, generate the identical hash. In mathematical notation, such a chosen-prefix collision can be written as 𝐻(𝑃‖𝑆)=𝐻(𝑃′‖𝑆′). The sort of collision assault is rather more highly effective as a result of it permits the attacker the liberty to create extremely custom-made forgeries.
For example the practicality and devastating penalties of the assault, Stevens, Lenstra, and de Weger used it to create two cryptographic X.509 certificates that generated the identical MD5 signature however totally different public keys and totally different Distinguished Identify fields. Such a collision may induce a certificates authority aspiring to signal a certificates for one area to unknowingly signal a certificates for a completely totally different, malicious area.
In 2008, a group of researchers that included Stevens, Lenstra, and de Weger demonstrated how a selected prefix assault on MD5 allowed them to create a rogue certificates authority that might generate TLS certificates that may be trusted by all main browsers. A key ingredient for the assault is software program named hashclash, developed by the researchers. Hashclash has since been made publicly accessible.
Regardless of the undisputed demise of MD5, the operate remained in widespread use for years. Deprecation of MD5 didn’t begin in earnest till 2012 after malware referred to as Flame, reportedly created collectively by the governments of Israel and the US, was discovered to have used a selected prefix assault to spoof MD5-based code signing by Microsoft’s Home windows replace mechanism. Flame used the collision-enabled spoofing to hijack the replace mechanism so the malware may unfold from system to system inside an contaminated community.
Greater than 12 years after Flame’s devastating injury was found and twenty years after collision susceptibility was confirmed, MD5 has felled one more extensively deployed know-how that has resisted frequent knowledge to maneuver away from the hashing scheme—the RADIUS protocol, which is supported in {hardware} or software program offered by at the very least 86 distinct distributors. The result’s “Blast RADIUS,” a fancy assault that permits an attacker with an energetic adversary-in-the-middle place to achieve administrator entry to gadgets that use RADIUS to authenticate themselves to a server.
“Surprisingly, within the twenty years since Wang et al. demonstrated an MD5 hash collision in 2004, RADIUS has not been up to date to take away MD5,” the analysis group behind Blast RADIUS wrote in a paper printed Tuesday and titled RADIUS/UDP Thought-about Dangerous. “In reality, RADIUS seems to have obtained notably little safety evaluation given its ubiquity in fashionable networks.”
The paper’s publication is being coordinated with safety bulletins from at the very least 90 distributors whose wares are weak. Most of the bulletins are accompanied by patches implementing short-term fixes, whereas a working group of engineers throughout the business drafts longer-term options. Anybody who makes use of {hardware} or software program that comes with RADIUS ought to learn the technical particulars offered later on this publish and examine with the producer for safety steering.

Getty Pictures
Some of the extensively used community protocols is weak to a newly found assault that may permit adversaries to achieve management over a variety of environments, together with industrial controllers, telecommunications companies, ISPs, and all method of enterprise networks.
Quick for Distant Authentication Dial-In Consumer Service, RADIUS harkens again to the times of dial-in Web and community entry by way of public switched phone networks. It has remained the de facto normal for light-weight authentication ever since and is supported in just about all switches, routers, entry factors, and VPN concentrators shipped prior to now twenty years. Regardless of its early origins, RADIUS stays a necessary staple for managing client-server interactions for:
- VPN entry
- DSL and Fiber to the House connections supplied by ISPs,
- Wi-Fi and 802.1X authentication
- 2G and 3G mobile roaming
- 5G Knowledge Community Identify authentication
- Cell information offloading
- Authentication over non-public APNs for connecting cell gadgets to enterprise networks
- Authentication to crucial infrastructure administration gadgets
- Eduroam and OpenRoaming Wi-Fi
RADIUS supplies seamless interplay between shoppers—sometimes routers, switches, or different home equipment offering community entry—and a central RADIUS server, which acts because the gatekeeper for consumer authentication and entry insurance policies. The aim of RADIUS is to supply centralized authentication, authorization, and accounting administration for distant logins.
The protocol was developed in 1991 by an organization referred to as Livingston Enterprises. In 1997 the Web Engineering Job Drive made it an official normal, which was up to date three years later. Though there’s a draft proposal for sending RADIUS site visitors inside a TLS-encrypted session that is supported by some distributors, many gadgets utilizing the protocol solely ship packets in clear textual content by way of UDP (Consumer Datagram Protocol).
XKCD
Goldberg et al.
Roll-your-own authentication with MD5? For actual?
Since 1994, RADIUS has relied on an improvised, home-grown use of the MD5 hash operate. First created in 1991 and adopted by the IETF in 1992, MD5 was on the time a preferred hash operate for creating what are referred to as “message digests” that map an arbitrary enter like a quantity, textual content, or binary file to a fixed-length 16-byte output.
For a cryptographic hash operate, it needs to be computationally unattainable for an attacker to search out two inputs that map to the identical output. Sadly, MD5 proved to be based mostly on a weak design: Inside just a few years, there have been indicators that the operate could be extra prone than initially thought to attacker-induced collisions, a deadly flaw that permits the attacker to generate two distinct inputs that produce similar outputs. These suspicions had been formally verified in a paper printed in 2004 by researchers Xiaoyun Wang and Hongbo Yu and additional refined in a analysis paper printed three years later.
The latter paper—printed in 2007 by researchers Marc Stevens, Arjen Lenstra, and Benne de Weger—described what’s referred to as a chosen-prefix collision, a sort of collision that outcomes from two messages chosen by an attacker that, when mixed with two extra messages, create the identical hash. That’s, the adversary freely chooses two distinct enter prefixes 𝑃 and 𝑃′ of arbitrary content material that, when mixed with rigorously corresponding suffixes 𝑆 and 𝑆′ that resemble random gibberish, generate the identical hash. In mathematical notation, such a chosen-prefix collision can be written as 𝐻(𝑃‖𝑆)=𝐻(𝑃′‖𝑆′). The sort of collision assault is rather more highly effective as a result of it permits the attacker the liberty to create extremely custom-made forgeries.
For example the practicality and devastating penalties of the assault, Stevens, Lenstra, and de Weger used it to create two cryptographic X.509 certificates that generated the identical MD5 signature however totally different public keys and totally different Distinguished Identify fields. Such a collision may induce a certificates authority aspiring to signal a certificates for one area to unknowingly signal a certificates for a completely totally different, malicious area.
In 2008, a group of researchers that included Stevens, Lenstra, and de Weger demonstrated how a selected prefix assault on MD5 allowed them to create a rogue certificates authority that might generate TLS certificates that may be trusted by all main browsers. A key ingredient for the assault is software program named hashclash, developed by the researchers. Hashclash has since been made publicly accessible.
Regardless of the undisputed demise of MD5, the operate remained in widespread use for years. Deprecation of MD5 didn’t begin in earnest till 2012 after malware referred to as Flame, reportedly created collectively by the governments of Israel and the US, was discovered to have used a selected prefix assault to spoof MD5-based code signing by Microsoft’s Home windows replace mechanism. Flame used the collision-enabled spoofing to hijack the replace mechanism so the malware may unfold from system to system inside an contaminated community.
Greater than 12 years after Flame’s devastating injury was found and twenty years after collision susceptibility was confirmed, MD5 has felled one more extensively deployed know-how that has resisted frequent knowledge to maneuver away from the hashing scheme—the RADIUS protocol, which is supported in {hardware} or software program offered by at the very least 86 distinct distributors. The result’s “Blast RADIUS,” a fancy assault that permits an attacker with an energetic adversary-in-the-middle place to achieve administrator entry to gadgets that use RADIUS to authenticate themselves to a server.
“Surprisingly, within the twenty years since Wang et al. demonstrated an MD5 hash collision in 2004, RADIUS has not been up to date to take away MD5,” the analysis group behind Blast RADIUS wrote in a paper printed Tuesday and titled RADIUS/UDP Thought-about Dangerous. “In reality, RADIUS seems to have obtained notably little safety evaluation given its ubiquity in fashionable networks.”
The paper’s publication is being coordinated with safety bulletins from at the very least 90 distributors whose wares are weak. Most of the bulletins are accompanied by patches implementing short-term fixes, whereas a working group of engineers throughout the business drafts longer-term options. Anybody who makes use of {hardware} or software program that comes with RADIUS ought to learn the technical particulars offered later on this publish and examine with the producer for safety steering.






