Are you aware what’s worse than discovering that your cellphone has some critical vulnerabilities? Discovering out that one of many vulnerabilities is actively being exploited by attackers. Through the newest month-to-month Pixel replace, Google famous that CVE-2024-32896 “could also be below restricted, focused exploitation.” The zero-day exploit (which merely implies that the vulnerability was unknown to the cellphone producer and no repair or patch was accessible when found) was listed within the Pixel Replace Bulletin as “Excessive Severity.”
In response to Forbes, this vulnerability has made the U.S. authorities so nervous that it’s ordering all federal workers with a Pixel handset to replace their telephones earlier than July 4th “or discontinue use of the product.” Whereas the warning is directed at U.S. authorities businesses, corporations may need to observe go well with; even people who use firm Wi-Fi to hook up with the web ought to set up the newest safety replace as quickly as doable.
The US authorities warning comes from the Recognized Exploited Vulnerabilities (KEV) listings which can be managed by CISA (Cybersecurity and Infrastructure Safety Company). The advisory stated, “Android Pixel incorporates an unspecified vulnerability within the firmware that permits for privilege escalation.” Privilege escalation would enable an attacker to make use of an app to seize data that usually wouldn’t be accessible to the dangerous actor.
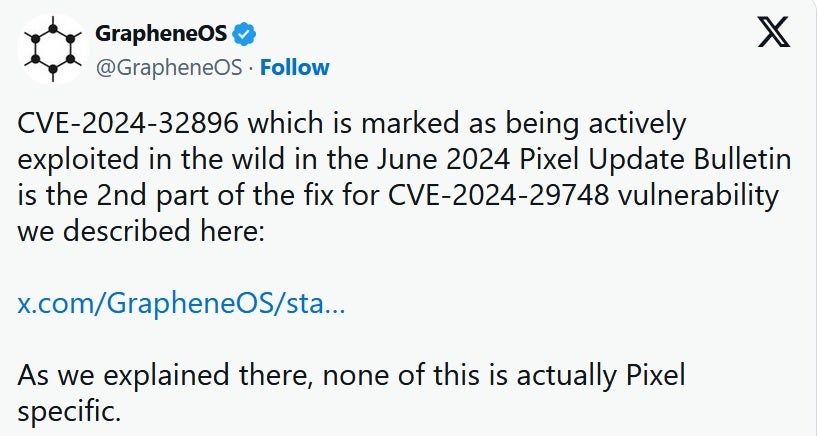
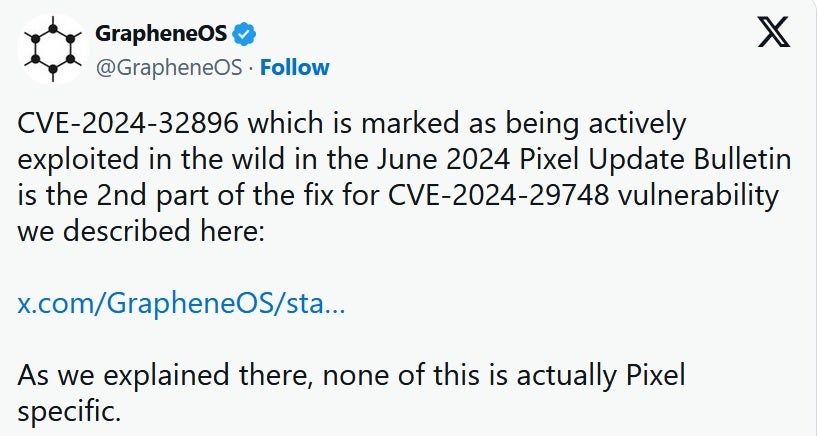
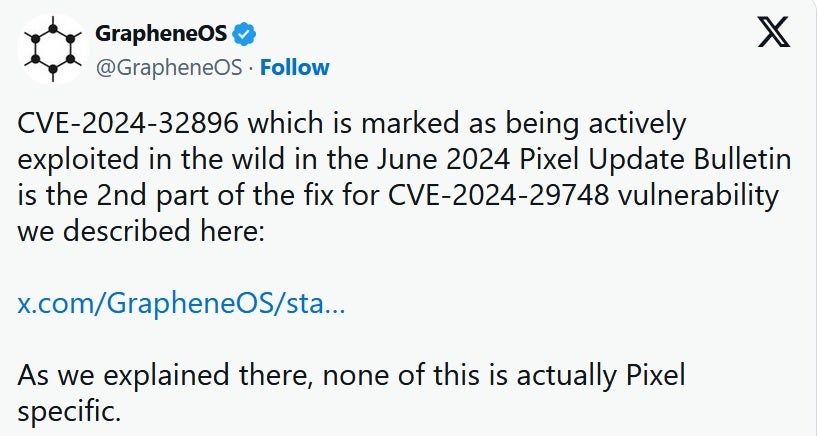
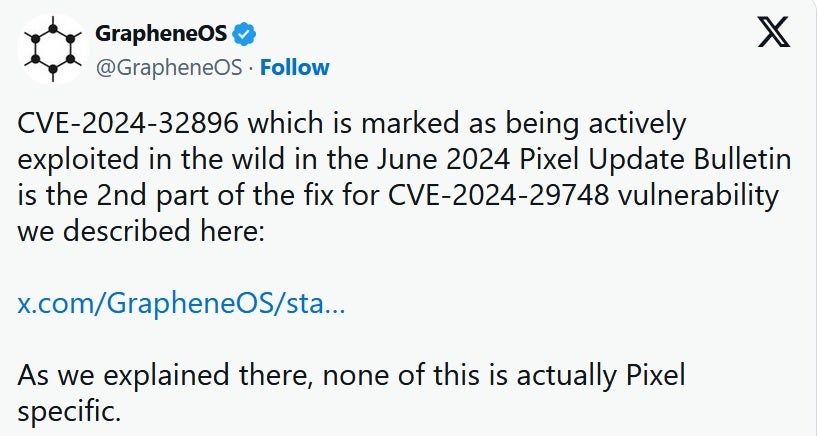
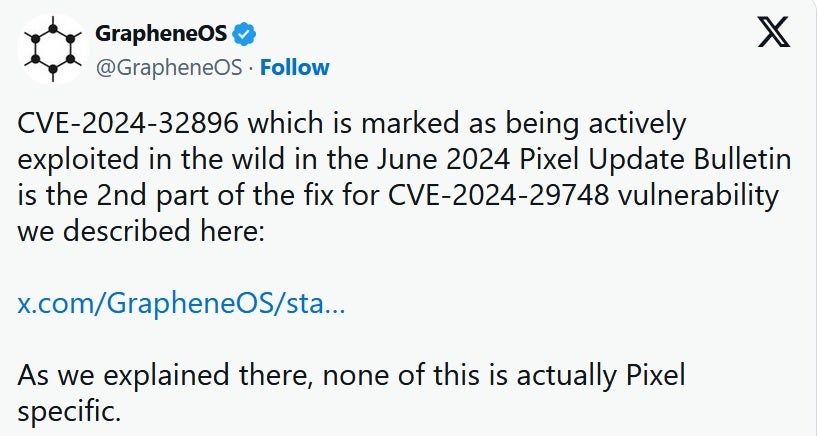
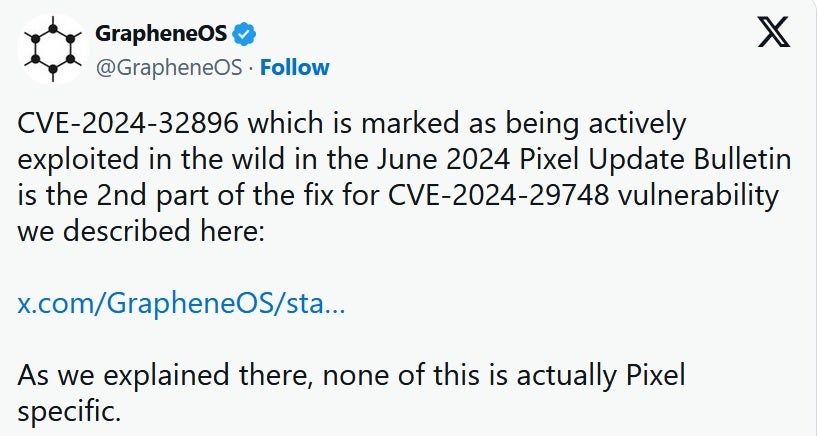
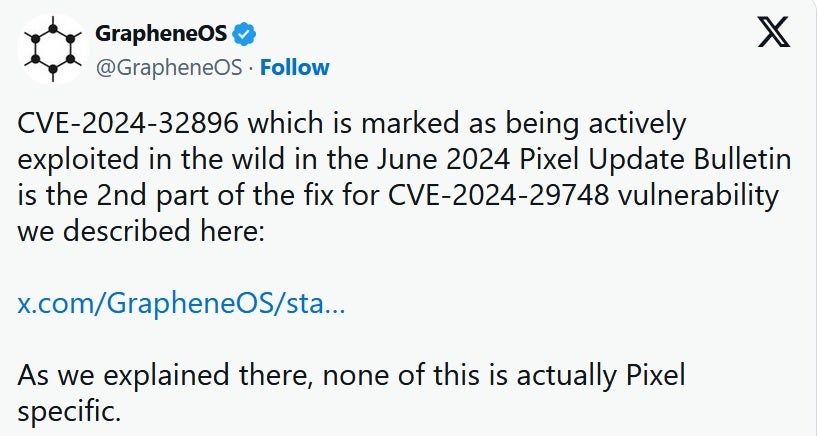
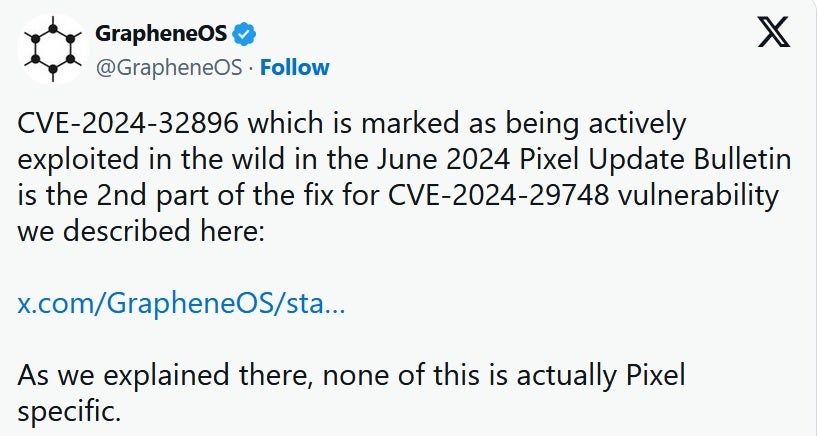
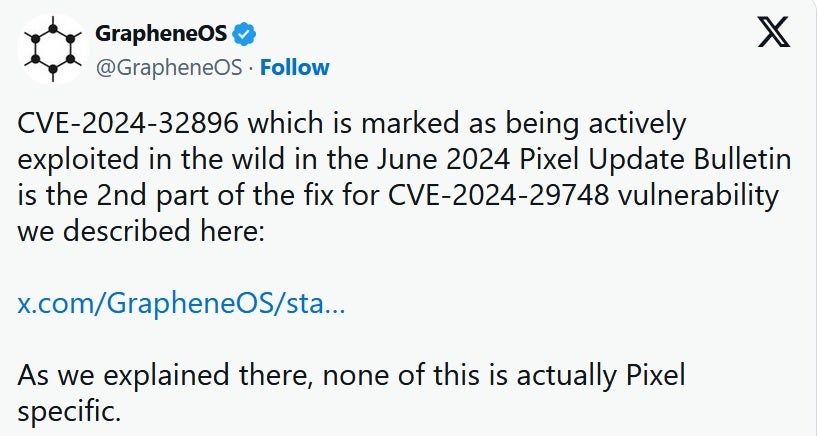
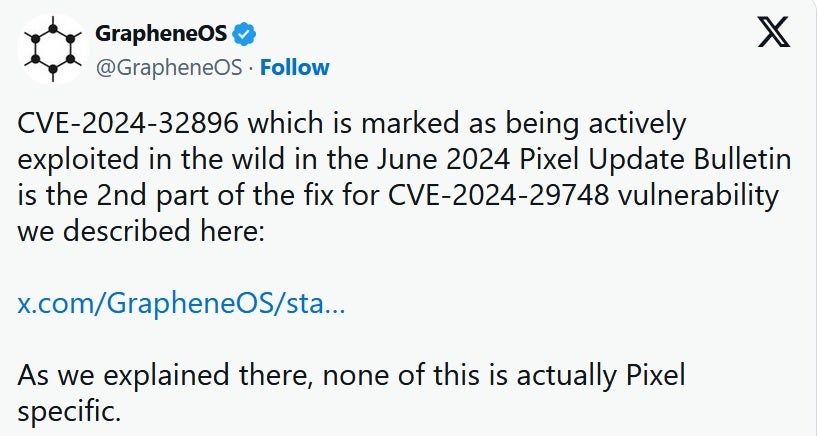
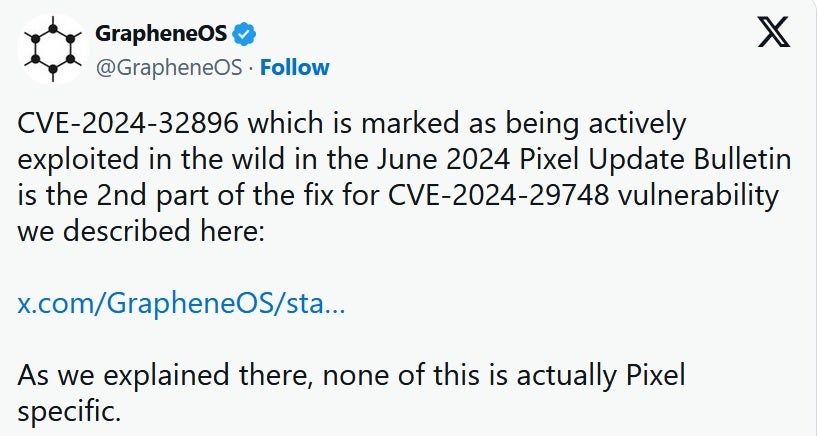
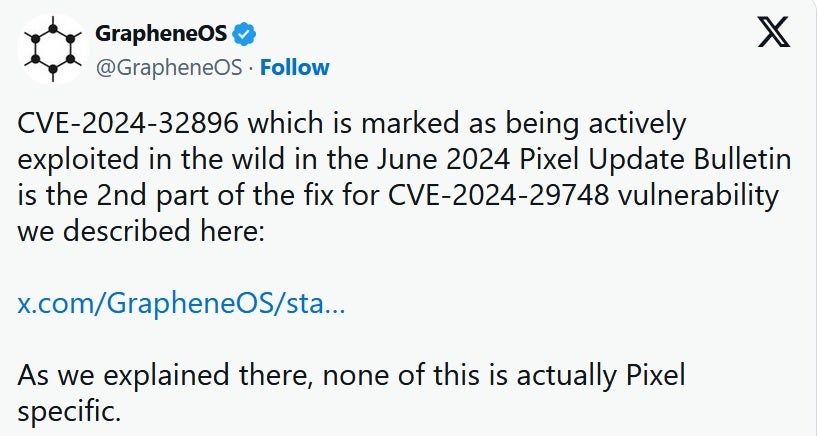
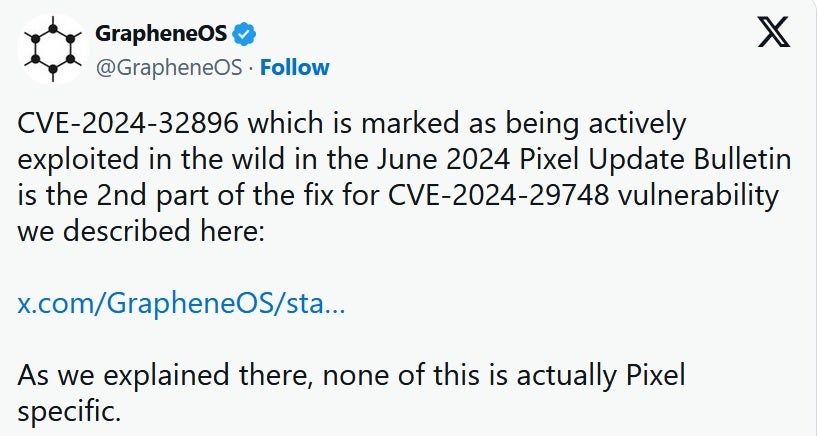
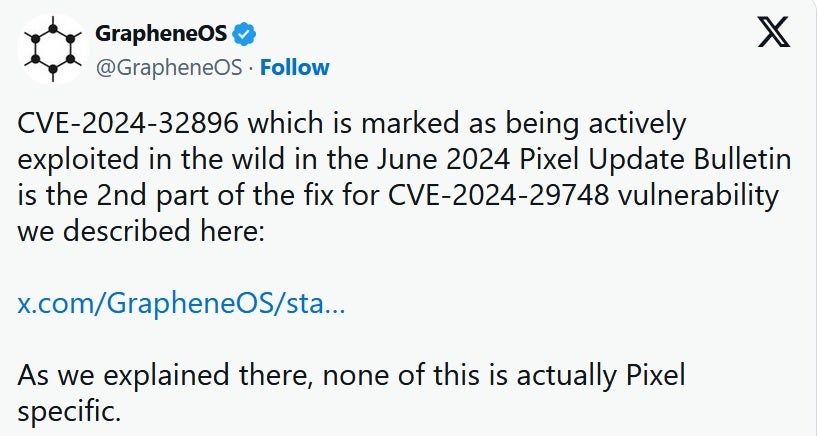
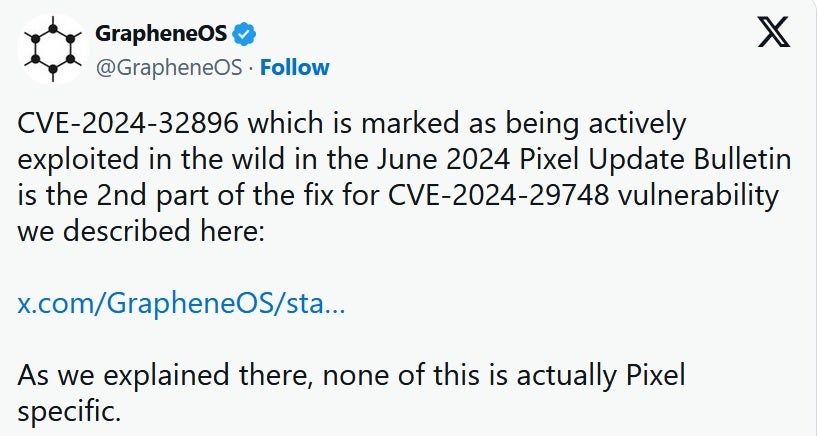
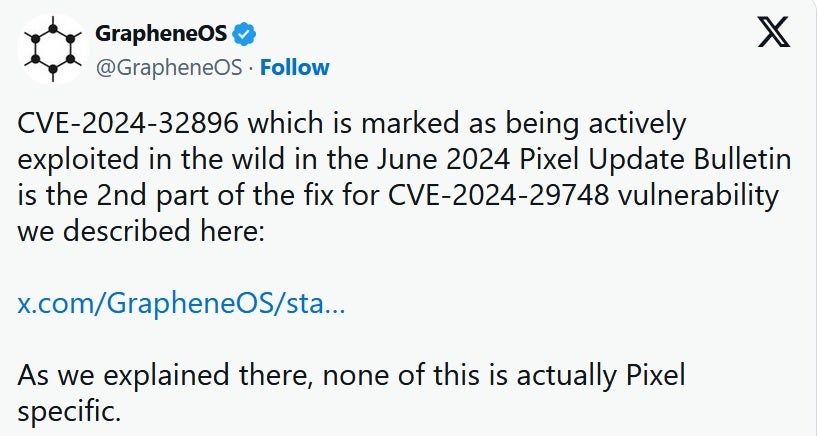
GrapheneOS posts extra details about the safety replace
Though the U.S. authorities appears targeted on Pixel customers, GrapheneOS says that the vulnerability is not only a concern for Pixel customers. Graphene OS says, “It is fastened on Pixels with the June replace (Android 14 QPR3) and will probably be fastened on different Android gadgets once they finally replace to Android 15. If they do not replace to Android 15, they in all probability will not get the repair, because it has not been backported.”
To replace your Pixel, go to Settings > System > Software program updates and in case you have an replace pending, merely observe the instructions. In a state of affairs like this, we might recommend that each one Pixel customers, whether or not they work for the U.S. authorities or not, replace their telephones straight away.
Are you aware what’s worse than discovering that your cellphone has some critical vulnerabilities? Discovering out that one of many vulnerabilities is actively being exploited by attackers. Through the newest month-to-month Pixel replace, Google famous that CVE-2024-32896 “could also be below restricted, focused exploitation.” The zero-day exploit (which merely implies that the vulnerability was unknown to the cellphone producer and no repair or patch was accessible when found) was listed within the Pixel Replace Bulletin as “Excessive Severity.”
In response to Forbes, this vulnerability has made the U.S. authorities so nervous that it’s ordering all federal workers with a Pixel handset to replace their telephones earlier than July 4th “or discontinue use of the product.” Whereas the warning is directed at U.S. authorities businesses, corporations may need to observe go well with; even people who use firm Wi-Fi to hook up with the web ought to set up the newest safety replace as quickly as doable.
The US authorities warning comes from the Recognized Exploited Vulnerabilities (KEV) listings which can be managed by CISA (Cybersecurity and Infrastructure Safety Company). The advisory stated, “Android Pixel incorporates an unspecified vulnerability within the firmware that permits for privilege escalation.” Privilege escalation would enable an attacker to make use of an app to seize data that usually wouldn’t be accessible to the dangerous actor.
GrapheneOS posts extra details about the safety replace
Though the U.S. authorities appears targeted on Pixel customers, GrapheneOS says that the vulnerability is not only a concern for Pixel customers. Graphene OS says, “It is fastened on Pixels with the June replace (Android 14 QPR3) and will probably be fastened on different Android gadgets once they finally replace to Android 15. If they do not replace to Android 15, they in all probability will not get the repair, because it has not been backported.”
To replace your Pixel, go to Settings > System > Software program updates and in case you have an replace pending, merely observe the instructions. In a state of affairs like this, we might recommend that each one Pixel customers, whether or not they work for the U.S. authorities or not, replace their telephones straight away.
Are you aware what’s worse than discovering that your cellphone has some critical vulnerabilities? Discovering out that one of many vulnerabilities is actively being exploited by attackers. Through the newest month-to-month Pixel replace, Google famous that CVE-2024-32896 “could also be below restricted, focused exploitation.” The zero-day exploit (which merely implies that the vulnerability was unknown to the cellphone producer and no repair or patch was accessible when found) was listed within the Pixel Replace Bulletin as “Excessive Severity.”
In response to Forbes, this vulnerability has made the U.S. authorities so nervous that it’s ordering all federal workers with a Pixel handset to replace their telephones earlier than July 4th “or discontinue use of the product.” Whereas the warning is directed at U.S. authorities businesses, corporations may need to observe go well with; even people who use firm Wi-Fi to hook up with the web ought to set up the newest safety replace as quickly as doable.
The US authorities warning comes from the Recognized Exploited Vulnerabilities (KEV) listings which can be managed by CISA (Cybersecurity and Infrastructure Safety Company). The advisory stated, “Android Pixel incorporates an unspecified vulnerability within the firmware that permits for privilege escalation.” Privilege escalation would enable an attacker to make use of an app to seize data that usually wouldn’t be accessible to the dangerous actor.
GrapheneOS posts extra details about the safety replace
Though the U.S. authorities appears targeted on Pixel customers, GrapheneOS says that the vulnerability is not only a concern for Pixel customers. Graphene OS says, “It is fastened on Pixels with the June replace (Android 14 QPR3) and will probably be fastened on different Android gadgets once they finally replace to Android 15. If they do not replace to Android 15, they in all probability will not get the repair, because it has not been backported.”
To replace your Pixel, go to Settings > System > Software program updates and in case you have an replace pending, merely observe the instructions. In a state of affairs like this, we might recommend that each one Pixel customers, whether or not they work for the U.S. authorities or not, replace their telephones straight away.
Are you aware what’s worse than discovering that your cellphone has some critical vulnerabilities? Discovering out that one of many vulnerabilities is actively being exploited by attackers. Through the newest month-to-month Pixel replace, Google famous that CVE-2024-32896 “could also be below restricted, focused exploitation.” The zero-day exploit (which merely implies that the vulnerability was unknown to the cellphone producer and no repair or patch was accessible when found) was listed within the Pixel Replace Bulletin as “Excessive Severity.”
In response to Forbes, this vulnerability has made the U.S. authorities so nervous that it’s ordering all federal workers with a Pixel handset to replace their telephones earlier than July 4th “or discontinue use of the product.” Whereas the warning is directed at U.S. authorities businesses, corporations may need to observe go well with; even people who use firm Wi-Fi to hook up with the web ought to set up the newest safety replace as quickly as doable.
The US authorities warning comes from the Recognized Exploited Vulnerabilities (KEV) listings which can be managed by CISA (Cybersecurity and Infrastructure Safety Company). The advisory stated, “Android Pixel incorporates an unspecified vulnerability within the firmware that permits for privilege escalation.” Privilege escalation would enable an attacker to make use of an app to seize data that usually wouldn’t be accessible to the dangerous actor.
GrapheneOS posts extra details about the safety replace
Though the U.S. authorities appears targeted on Pixel customers, GrapheneOS says that the vulnerability is not only a concern for Pixel customers. Graphene OS says, “It is fastened on Pixels with the June replace (Android 14 QPR3) and will probably be fastened on different Android gadgets once they finally replace to Android 15. If they do not replace to Android 15, they in all probability will not get the repair, because it has not been backported.”
To replace your Pixel, go to Settings > System > Software program updates and in case you have an replace pending, merely observe the instructions. In a state of affairs like this, we might recommend that each one Pixel customers, whether or not they work for the U.S. authorities or not, replace their telephones straight away.
Are you aware what’s worse than discovering that your cellphone has some critical vulnerabilities? Discovering out that one of many vulnerabilities is actively being exploited by attackers. Through the newest month-to-month Pixel replace, Google famous that CVE-2024-32896 “could also be below restricted, focused exploitation.” The zero-day exploit (which merely implies that the vulnerability was unknown to the cellphone producer and no repair or patch was accessible when found) was listed within the Pixel Replace Bulletin as “Excessive Severity.”
In response to Forbes, this vulnerability has made the U.S. authorities so nervous that it’s ordering all federal workers with a Pixel handset to replace their telephones earlier than July 4th “or discontinue use of the product.” Whereas the warning is directed at U.S. authorities businesses, corporations may need to observe go well with; even people who use firm Wi-Fi to hook up with the web ought to set up the newest safety replace as quickly as doable.
The US authorities warning comes from the Recognized Exploited Vulnerabilities (KEV) listings which can be managed by CISA (Cybersecurity and Infrastructure Safety Company). The advisory stated, “Android Pixel incorporates an unspecified vulnerability within the firmware that permits for privilege escalation.” Privilege escalation would enable an attacker to make use of an app to seize data that usually wouldn’t be accessible to the dangerous actor.
GrapheneOS posts extra details about the safety replace
Though the U.S. authorities appears targeted on Pixel customers, GrapheneOS says that the vulnerability is not only a concern for Pixel customers. Graphene OS says, “It is fastened on Pixels with the June replace (Android 14 QPR3) and will probably be fastened on different Android gadgets once they finally replace to Android 15. If they do not replace to Android 15, they in all probability will not get the repair, because it has not been backported.”
To replace your Pixel, go to Settings > System > Software program updates and in case you have an replace pending, merely observe the instructions. In a state of affairs like this, we might recommend that each one Pixel customers, whether or not they work for the U.S. authorities or not, replace their telephones straight away.
Are you aware what’s worse than discovering that your cellphone has some critical vulnerabilities? Discovering out that one of many vulnerabilities is actively being exploited by attackers. Through the newest month-to-month Pixel replace, Google famous that CVE-2024-32896 “could also be below restricted, focused exploitation.” The zero-day exploit (which merely implies that the vulnerability was unknown to the cellphone producer and no repair or patch was accessible when found) was listed within the Pixel Replace Bulletin as “Excessive Severity.”
In response to Forbes, this vulnerability has made the U.S. authorities so nervous that it’s ordering all federal workers with a Pixel handset to replace their telephones earlier than July 4th “or discontinue use of the product.” Whereas the warning is directed at U.S. authorities businesses, corporations may need to observe go well with; even people who use firm Wi-Fi to hook up with the web ought to set up the newest safety replace as quickly as doable.
The US authorities warning comes from the Recognized Exploited Vulnerabilities (KEV) listings which can be managed by CISA (Cybersecurity and Infrastructure Safety Company). The advisory stated, “Android Pixel incorporates an unspecified vulnerability within the firmware that permits for privilege escalation.” Privilege escalation would enable an attacker to make use of an app to seize data that usually wouldn’t be accessible to the dangerous actor.
GrapheneOS posts extra details about the safety replace
Though the U.S. authorities appears targeted on Pixel customers, GrapheneOS says that the vulnerability is not only a concern for Pixel customers. Graphene OS says, “It is fastened on Pixels with the June replace (Android 14 QPR3) and will probably be fastened on different Android gadgets once they finally replace to Android 15. If they do not replace to Android 15, they in all probability will not get the repair, because it has not been backported.”
To replace your Pixel, go to Settings > System > Software program updates and in case you have an replace pending, merely observe the instructions. In a state of affairs like this, we might recommend that each one Pixel customers, whether or not they work for the U.S. authorities or not, replace their telephones straight away.
Are you aware what’s worse than discovering that your cellphone has some critical vulnerabilities? Discovering out that one of many vulnerabilities is actively being exploited by attackers. Through the newest month-to-month Pixel replace, Google famous that CVE-2024-32896 “could also be below restricted, focused exploitation.” The zero-day exploit (which merely implies that the vulnerability was unknown to the cellphone producer and no repair or patch was accessible when found) was listed within the Pixel Replace Bulletin as “Excessive Severity.”
In response to Forbes, this vulnerability has made the U.S. authorities so nervous that it’s ordering all federal workers with a Pixel handset to replace their telephones earlier than July 4th “or discontinue use of the product.” Whereas the warning is directed at U.S. authorities businesses, corporations may need to observe go well with; even people who use firm Wi-Fi to hook up with the web ought to set up the newest safety replace as quickly as doable.
The US authorities warning comes from the Recognized Exploited Vulnerabilities (KEV) listings which can be managed by CISA (Cybersecurity and Infrastructure Safety Company). The advisory stated, “Android Pixel incorporates an unspecified vulnerability within the firmware that permits for privilege escalation.” Privilege escalation would enable an attacker to make use of an app to seize data that usually wouldn’t be accessible to the dangerous actor.
GrapheneOS posts extra details about the safety replace
Though the U.S. authorities appears targeted on Pixel customers, GrapheneOS says that the vulnerability is not only a concern for Pixel customers. Graphene OS says, “It is fastened on Pixels with the June replace (Android 14 QPR3) and will probably be fastened on different Android gadgets once they finally replace to Android 15. If they do not replace to Android 15, they in all probability will not get the repair, because it has not been backported.”
To replace your Pixel, go to Settings > System > Software program updates and in case you have an replace pending, merely observe the instructions. In a state of affairs like this, we might recommend that each one Pixel customers, whether or not they work for the U.S. authorities or not, replace their telephones straight away.
Are you aware what’s worse than discovering that your cellphone has some critical vulnerabilities? Discovering out that one of many vulnerabilities is actively being exploited by attackers. Through the newest month-to-month Pixel replace, Google famous that CVE-2024-32896 “could also be below restricted, focused exploitation.” The zero-day exploit (which merely implies that the vulnerability was unknown to the cellphone producer and no repair or patch was accessible when found) was listed within the Pixel Replace Bulletin as “Excessive Severity.”
In response to Forbes, this vulnerability has made the U.S. authorities so nervous that it’s ordering all federal workers with a Pixel handset to replace their telephones earlier than July 4th “or discontinue use of the product.” Whereas the warning is directed at U.S. authorities businesses, corporations may need to observe go well with; even people who use firm Wi-Fi to hook up with the web ought to set up the newest safety replace as quickly as doable.
The US authorities warning comes from the Recognized Exploited Vulnerabilities (KEV) listings which can be managed by CISA (Cybersecurity and Infrastructure Safety Company). The advisory stated, “Android Pixel incorporates an unspecified vulnerability within the firmware that permits for privilege escalation.” Privilege escalation would enable an attacker to make use of an app to seize data that usually wouldn’t be accessible to the dangerous actor.
GrapheneOS posts extra details about the safety replace
Though the U.S. authorities appears targeted on Pixel customers, GrapheneOS says that the vulnerability is not only a concern for Pixel customers. Graphene OS says, “It is fastened on Pixels with the June replace (Android 14 QPR3) and will probably be fastened on different Android gadgets once they finally replace to Android 15. If they do not replace to Android 15, they in all probability will not get the repair, because it has not been backported.”
To replace your Pixel, go to Settings > System > Software program updates and in case you have an replace pending, merely observe the instructions. In a state of affairs like this, we might recommend that each one Pixel customers, whether or not they work for the U.S. authorities or not, replace their telephones straight away.